Connection begets connection. In 1999, 18 years ago, when just 4% of the world’s population was online, Kevin Ashton coined the term Internet of Things, Neil Gershenfeld of MIT Media Lab wrote the book “When Things Start to Think,” and Neil Gross wrote in BusinessWeek: “In the next century, planet Earth will don an electronic skin. It will use the internet as a scaffold to support and transmit its sensations. This skin is already being stitched together. It consists of millions of embedded electronic measuring devices: thermostats, pressure gauges, pollution detectors, cameras, microphones, glucose sensors, EKGs, electroencephalographs. These will probe and monitor cities and endangered species, the atmosphere, our ships, highways and fleets of trucks, our conversations, our bodies – even our dreams.”
He was right. Today, 49% of the world’s population is connected online and an estimated 8.4 billion connected things are in use worldwide.
The stickiness and value of a connected life will be far too strong for a significant number of people to have the will or means to disconnect. Anonymous respondent
The Internet of Things (IoT) is in full flower. The expanding collection of connected things goes mostly unnoticed by the public – sensors, actuators and other items completing tasks behind the scenes in day-to-day operations of businesses and government, most of them abetted by machine-to-machine “computiction” – that is, artificial-intelligence-enhanced communication. The most public items in the burgeoning IoT are cars, voice-activated assistants, appliances and other home systems, physician-prescribed or recommended health-monitoring devices, road sensors, public-safety and security devices, smart meters and personal fitness and health trackers for people and animals – dogs, cats, horses, cows and more. And then there are emerging IoT products that show how the urge to create connectivity extends to such prosaic items as toothbrushes, dental floss, hairbrushes, pillows, egg trays, wine bottle sleeves, baby monitors and changing tables, silverware, umbrellas, all manner of toys and sporting goods and remote-controlled pet food dispensers, to name a few.
The very connectedness of the IoT leaves it open to security and safety vulnerabilities. Every connected thing is susceptible to attack or misuse. In September 2016 at DEF CON, one of the world’s largest security conferences, 47 vulnerabilities affecting 23 IoT-enabled items (door locks, wheelchairs, thermostats and more) from 21 manufacturers were disclosed. Soon after, there was a massive distributed denial-of-service (DDoS) attack on Oct. 21, 2016, against Dyn, an internet performance management company. The attack was accomplished when tens of millions of IoT-connected devices like printers, DVRs, cable set-top boxes, webcams and baby monitors were used to launch the DDoS and block Dyn’s ability to connect internet users to the web addresses they hoped to access, such as Twitter, Amazon, PayPal, Spotify, Netflix, HBO, The Wall Street Journal and The New York Times. A simple software program called Mirai was used to create the botnet that initiated the attack.
After the Dyn attack, a report in The New York Times called the IoT a “weapon of mass disruption.” While that assault amounted to nothing more than a short-lived slowdown of a large portion of the internet, it showed how vulnerable connected devices are to hacking and exploitation. In recent weeks, a ransomware attack named WannaCry affected computers in 150 countries, and its creators demanded payments from those whose computers were compromised before releasing their files. Experts pointed out how dramatically this attack highlighted the vulnerabilities of the IoT.
Researchers have been showing how easy it is to hack cars, voting machines and power plants. They have demonstrated ransomware exploits against home thermostats and exposed vulnerabilities in implanted heart pacemakers. In one paper, “IoT Goes Nuclear,” analysts showed how a flaw in the design of smart lightbulbs could be used for a “bricking attack” that kills all of a city’s traffic lights. Within the past year Bryan Johnson (Kernal), Elon Musk (Neuralink) and Mark Zuckerberg (Facebook’s Building 8) have announced initiatives to create an effective consumer-grade brain-computer interface thus, of course, hacking a person’s brain could also be a future security issue.
All of this has prompted concern among internet security experts, including Bruce Schneier, who delivered a fiery speech at the Organization for Economic Cooperation and Development’s Digital Economy Ministerial Meeting in Cancun, Mexico, in June 2016. He predicted that unless technology-based businesses and governments address these problems, there might be a flight from connectivity – that is, people could start retreating offline as risks mount. “My guess is we are reaching the high-water mark of computerization and connectivity,” he said, “and in a few years we are going to be deciding what to connect and what to disconnect and become more realistic about what can work. We are creating a society by which a totalitarian government can control everything. Right now it’s more power to the powerful. And we are living in a computerized world where attacks are easier to create than defenses against them. This is coming faster than we think. We need to address it now. People up to now have been able to code the world as they see fit. That has to change. We have to make moral, ethical and political decisions about how these things should work and then put that into our code. Politicians and technologists still talk past each other. This has to change.”
Thus, the question: Could security vulnerabilities that become evident as the IoT rolls out prompt people, businesses and government to avoid or withdraw from certain online connectivity options? In summer 2016, Pew Research Center and Elon University’s Imagining the Internet Center conducted a large canvassing of technologists, scholars, practitioners, strategic thinkers and other leaders, asking them to react to this framing of the issue:
As billions more everyday objects are connected in the Internet of Things, they are sending and receiving data that enhances local, national and global systems as well as individuals’ lives. But such connectedness also creates exploitable vulnerabilities. As automobiles, medical devices, smart TVs, manufacturing equipment and other tools and infrastructure are networked, is it likely that attacks, hacks or ransomware concerns in the next decade will cause significant numbers of people to decide to disconnect, or will the trend toward greater connectivity of objects and people continue unabated?
Some 1,201 responded to this nonscientific canvassing: 15% of these particular respondents said significant numbers would disconnect and 85% chose the option that most people will move more deeply into connected life. (See “About this canvassing of experts” for further details about the limits of this sample.)
Participants were asked to explain their answers and were offered the following prompts to consider:
- What is the most likely kind of physical or human damage that will occur when things are networked?
- How might governments and technologists respond to make things more secure and safe?
- Is it possible to network physical objects in such a way that they will generally remain safe for the vast majority most of the time?
Several broad assertions and assumptions underpinned many respondents’ answers:
[Terry]
Further, these experts note there is commercial incentive to add this feature to as many gadgets and aspects of life as possible. A sharp description of this dynamic came from Ian O’Byrne, assistant professor of literacy education at the College of Charleston, who said, “More people will become connected because device manufacturers will make it far easier and acceptable to purchase and use these devices. In the same fashion that we added electricity to every device possible with advances in technology, manufacturers will ‘add the internet’ to all devices in the attempt to make them better … but also possibly sell more product. In short, more people and devices will be connected.”
Connectivity has many exploitable flaws: Many respondents, including those arguing the case that more connectivity will unfold, outlined downsides to hyper-connectivity. They maintained that defects and vulnerabilities are a natural part of quickly evolving networks, and software and hardware and security responses are always a step behind. Many believe that ongoing attacks are inevitable in all networked digital systems, and there will be large-scale problems in coordinating various elements of the IoT to get them to work together. While these experts expect that living an IoT-dependent life will be scary at times and often frustrating, most do not expect this will be enough to deter most people from diving deeper into connectivity.
For instance, an anonymous professor of information and history at a state university explained, “People can get used to anything, and – just as with terrorism – the inevitable occasional damage from deliberate or inadvertent failures in highly networked systems will become routine. Occasional terrorism using Internet of Things connections is very likely, shutting down infrastructure, hospitals, businesses, etc. Hackers will always find vulnerabilities in highly networked systems, and technical fixes will not change that.” An anonymous professor at MIT observed, “We will live in a world of ambivalent participation.”
This new connectivity jeopardizes humans and physical infrastructure, not just communication: A recurring refrain in these experts’ answers is that the IoT poses significant new problems because messing with IoT-linked devices can cause real-world damage. Schneier has described it this way: “With the advent of the Internet of Things and cyberphysical systems in general, we’ve given the internet hands and feet: the ability to directly affect the physical world. What used to be attacks against data and information have become attacks against flesh, steel and concrete.”
Barry Chudakov, founder and principal at Sertain Research and StreamFuzion Corp., wrote, “We are witnessing the advent of what the brilliant scholar and media theorist Derrick de Kerckhove (years ago) called ‘connected intelligence’ – but on a scale unimaginable before the 21st century. … De Kerckhove called it a ‘change of being,’ which captures the breadth and depth of what is happening daily as our physical and digital objects intertwine. So not only will the trend toward greater connectivity of people and objects continue, it will continue to change boundaries and dynamics of all sorts – personal, social, moral, political. … The IoT reality represents both huge opportunity and huge vulnerability. They go hand in hand. We cannot be proactive until we educate ourselves and continue to educate others about what is required to secure IoT and what secure IoT practices entail.”
Many participants in this canvassing wrote detailed elaborations explaining their positions. Some chose to have their names connected to their answers; others opted to respond anonymously. These findings do not represent all possible points of view, but they do reveal a wide range of striking observations. Respondents collectively articulated seven major themes that are introduced and explained below and expanded upon in sections that begin later in this report.
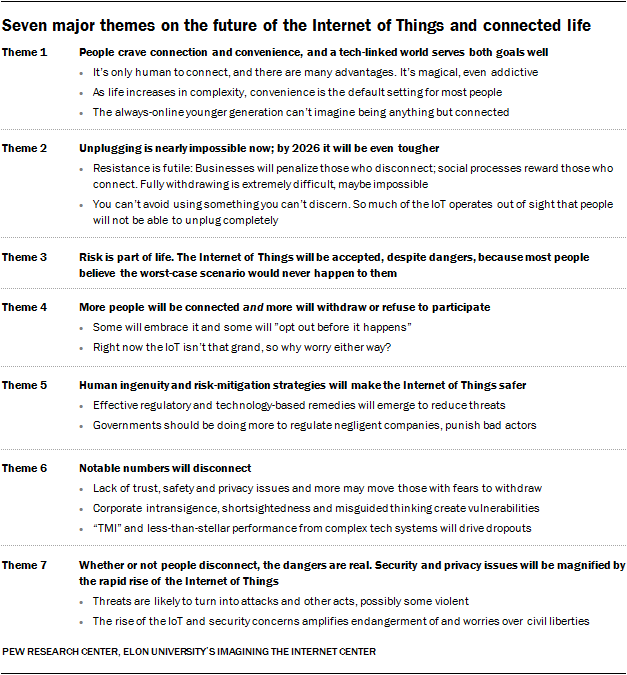
The following section presents a brief overview of the most evident themes extracted from the written responses, including a small selection of representative quotes supporting each point. Some responses are lightly edited for style or due to length.
Theme 1: People crave connection and convenience, and a tech-linked world serves both goals well
We have a deep need and desire to connect. … I see no evidence for a reversal of that trend. Peter Morville
The vast majority of expert respondents to this research study, as well as to a previous study on attitudes about the future of the Internet of Things by Pew Research Center and Imagining the Internet, agree that the IoT will continue apace, expanding vastly in size and influence over the next decade. They say businesses expect to reap large dividends from the advancement of the IoT and that people are naturally driven to connect to other people, information and services. Further, they argue that society reaps benefits from connected infrastructure and objects – from transportation, communications and business and industrial systems to individual products and services. Additionally, as modern life becomes more complicated, these respondents argue that people count on convenience to conquer chaos and they enjoy experimenting with magical new tools. Their desire for new gadgetry often outweighs any perceived risks.
It’s only human to connect, and there are many advantages. It’s magical, even addictive
Robert Bell, co-founder of the Intelligent Community Forum, wrote, “Because connected life offers so many opportunities in terms of cost savings, entertainment, news and public participation, people will keep moving into it.”
The magical behaviors that the new devices will provide will be too strong for people to resist. David Wuertele
David Clark, senior research scientist at MIT and Internet Hall of Fame member, replied, “Unless we have a disaster that triggers a major shift in usage, the convenience and benefits of connectivity will continue to attract users. Evidence suggests that people value convenience today over possible future negative outcomes.”
Jim Warren, longtime technology entrepreneur and activist, replied, “From the beginning of any kind of ‘connectivity’ between humans (both biological and corporate 😉 – from primitive Man to the present – we have almost always favored and pursued increased connectivity. It is the essence of society, culture, productivity, improved living and lifestyle alternatives (et al.) and will continue. Probably the largest deterrents to the speed and pervasiveness of its development will be largely, perhaps mostly, how much it costs its users, both financially and functionally.”
Mark Lemley, a professor at Stanford Law School, commented, “There will definitely be hacks and other problems, just as there are with credit cards and financial information online today. But the advantages of connectivity are just too great for people to forgo it. We may see greater local control over when connected devices are enabled, allowing people to turn connectivity off at will.”
Peter Morville, president of Semantic Studios, said, “We have a deep need and desire to connect. Everything in the history of communication technology suggests we will take advantage of every opportunity to connect more richly and deeply. I see no evidence for a reversal of that trend.”
Bart Knijnenburg, an assistant professor in human-centered computing at Clemson University, responded, “The immediate and concrete benefits of connectivity, however small, will outweigh the uncertain future threats, so people will choose connectivity over security. Insurance firms may capitalize on insuring against digital threats to physical devices. The only thing that may cause people to disconnect is a widespread terrorist attack against the digital infrastructure. Even if such an attack is inconsequential for people’s TVs and fridges, it may change the narrative enough that people will disconnect.”
Some respondents pointed out that people are attracted to shiny new tech tools, services, platforms and systems even at times when this could become fatal attraction. There are people of all ages who find that connectivity “is addictive,” one anonymous respondent and others argued. Richard J. Perry, a respondent who did not share additional identifying details, commented, “Great damage is possible and governments and vendors will strive to improve security but will fail. Internet insecurity will be the rule, not the exception. But we are addicted and will not surrender this.”
David Wuertele, a software engineer at Tesla Motors, replied, “The magical behaviors that the new devices will provide will be too strong for people to resist. Even though many of these IoT devices have no real need to be connected to the cloud, and even though connecting them to the cloud presents a real risk to people, there is not enough of a force to ‘clean up’ the implementations. The desire by people for these magic devices is so strong that they will sign away their own personal data as well as their families’ (and sometimes their friends’) data to get the goodies.”
An anonymous respondent observed, “People are influenced by gee-whiz gizmos, frequently at the expense of safety.”
As life increases in complexity, convenience is the default setting for most people
Many respondents pointed out that people generally opt for what appears to be the best route to efficiency and expediency as they adopt technology. Paul Jones, clinical professor and director at the University of North Carolina, optimistically predicted, “The Law of Least Effort applies to the Internet of Things. Short of massive social and political changes, we will become more connected, more networked and happier that we are.”
There are few examples in human history of people making rational decisions about privacy or security. Nathaniel Borenstein
An anonymous respondent who is concerned about the downsides of connectivity responded, “People will trade their safety for convenience. They always have. They always will.” And Nathaniel Borenstein, chief scientist at Mimecast, said, “There are few examples in human history of people making rational decisions about privacy or security.”
Matt Bates, a programmer and concept artist at Jambeeno Ltd., commented, “I expect the following are and will always be true with regard to internet connectivity: Convenience > privacy. Convenience > statistically infrequent health consequences. Convenience > statistically infrequent financial problems. For a minority, one or more of the above will be reversed and they will stand out as oddities in an increasingly connected world (note, e.g., code and security expert Dan Geer, part of the CIA apparatus, who doesn’t use a cellphone). … I think most networked physical objects are ‘safe for the vast majority most of the time.’ It’s what happens with the aggregation of networked objects that is most concerning, and then it will usually be most deleterious to a minority of the population. There’s probably no way to get around this short of not networking things. Convenience will out. Sadly.”
Sunil Paul, entrepreneur, investor and activist at Spring Ventures, observed, “Convenience and ‘magic’ will overwhelm concerns. The history of technology is clear on this front – ATMs, e-commerce, credit cards, the list is endless.”
Julie Gomoll, CEO of Julie Gomoll Inc., wrote, “Hacks and ransomware won’t matter. We have those now, and very few people disconnect as a result. There will be lots of junk things – ‘We need a networked thing!’ will be the new ‘We need an app!’ There will be new kinds of hacks and attacks, and we’ll figure out how to stop them. We’ll discover unintended consequences, attribute them to growing pains. And we will never, ever disconnect.”
The always-on younger generation can’t imagine being anything but connected
A number of respondents said they expect the younger generation, accustomed from the start to trust in technology with few doubts, is likely to adopt the IoT, warts and all. Jan Schaffer, executive director of J-Lab: The Institute for Interactive Journalism, said youth will stay connected because they are too invested in the IoT to leave it. “Young people will continue to deeply connect until they have assets and identities that they care about and don’t want to put at risk,” she wrote.
To today’s 10-year-old the idea of a watch that can’t take basic health information is like a 20-year-old trying to understand what the hell a cassette tape is. Anonymous respondent
Lisa Heinz, doctoral student at Ohio University, observed, “Young people are perpetually connected to each other, so much so they might not know how to exist without the internet that enables that connection. As our homes become a part of that connection in even the tiniest of automated ways, we will no longer care how it works, just that it works as expected. Thus, a mass migration away from a connected society is unlikely.”
Some respondents said most younger people don’t know how to live any other way. An anonymous respondent commented, “The individuals who will be using this technology are the teens of today. It will be second-nature for them to use and interact daily across many devices and modalities.” Another anonymous respondent replied, “Generations now take the internet for granted. They can’t cope without it.”
Another anonymous respondent wrote, “If today’s adults don’t get more connected, the next generation will. To today’s 10-year-old the idea of a watch that can’t take basic health information is like a 20-year-old trying to understand what the hell a cassette tape is.”
Theme 2: Unplugging isn’t easy now, and by 2026 it will be even tougher
Many respondents made the argument that disconnecting resigns people to relative isolation and some level of deprivation. They say it is not a realistic option for most people to live this life. An anonymous respondent replied, “It is becoming increasingly difficult to disconnect, even in the midst of threats and distrust. To be an active, engaged member of society, it is now virtually impossible to be completely unplugged.” Another anonymous respondent said, “There will be an increasing attempt to remain unconnected or disconnect, but it will be increasingly impossible to live that way.” And an anonymous chairman and CEO at a nonprofit organization observed, “We will continue to become more connected without realizing our critical growing dependence.”
They also made the case that the marketplace for non-connected devices will shrink in the future, often leaving consumers with little choice but to accept an IoT presence in their lives. And they pointed out that even now people are often using connected devices, tools or services without knowing they are connected. An anonymous participant observed, “It will be increasingly difficult to unplug, as more and more aspects of ordinary daily life are plugged in. Unplugging will require a religious level of commitment.”
Resistance is futile: Businesses will penalize those who disconnect; social processes reward those who connect. Fully withdrawing is extremely difficult, maybe impossible
A number of respondents observed that the usefulness and “stickiness” of IoT platforms and services plus the corporate imperative to strive for constantly rising profits will drive IoT decision-making, causing businesses to operate in such a fashion as to make it increasingly difficult if not impossible for people to choose to opt out and still access services and functions.
There is no choice but to become ever more networked and connected: Capital will demand it. Anonymous law professor
Andrew Walls, managing vice president at Gartner, replied, “The benefits of IoT to the vendors of products and services will overwhelm the objections of the few consumers who fear security issues. Pricing models will penalize those who attempt to disconnect and reward those who connect. … If IoT enhances performance against consumer variables for selection/purchase, IoT integration will expand massively.”
Adam Nelson, chief technology officer at Factr, commented, “People won’t be able to disconnect. Manufacturers won’t build in the functionality to do it.”
Mary K. Pratt, a freelance technology journalist, commented, “Even if individuals are concerned about the risks, they’ll find it difficult or impossible to opt out of these connections if they want to continue with the products or services they want and/or need.” An anonymous law professor at a state university observed, “There is no choice but to become ever more networked and connected: Capital will demand it.”
Several respondents likened those adopting IoT products and services to livestock. An anonymous respondent observed, “‘Moo,’ say the cattle.” And an anonymous professor at a state university said, “Those who want to fleece the sheep will get the sheep to come on in.” An anonymous chief scientist emeritus for one of the top technology innovation companies in the U.S. said, “Think sheep.”
[to disconnect]
Joseph Turow, a communications professor at the University of Pennsylvania, said, “Despite hacks and privacy issues, people will feel a need to keep connected, partly because companies will reward them for doing so (or make life difficult if they don’t). People will feel resigned to navigating an environment where data are key coins of exchange.”
Respondents resoundingly agreed that people are already dependent upon this vastly growing network, as it enables so many systems and helps so many people in successfully getting through each day. The IoT becomes more complex, more important and more difficult to disconnect from every day.
An anonymous respondent said, “People will have to be networked, because to be otherwise will mean difficulties getting employment, health care and other services that are necessary.” Randy Albelda, an economics professor at the University of Massachusetts, Boston, agreed: “At this point I see no way out. If I disconnect, I in effect lose my job and/or pay a lot more money and/or spend an enormous amount of time living my daily life. The toothpaste is out of the tube.”
[Transportation Security Administration]
Michael Whitaker, vice president of emerging solutions at ICF International, replied, “The inevitable march to a more-connected life will continue unabated for two reasons. 1) An increasing amount of technology will emerge that is connected by default and the onus will be on users to disconnect (rather than connect). Most users, even if concerned about vulnerabilities, will not proactively disconnect across all of their devices. 2) The general understanding of the public related to the vulnerability of connected devices will remain low. They will be sold on the benefits (of which there are many) with few voices echoing the risks. Barring an awareness-altering event, people will generally think less and less about their connectivity over the next decade and will come to expect connectivity as the default state.”
Naomi Baron, a linguistics professor at American University, commented, “The issue is less about what choices individuals wish to make than about the choices that institutions or other individuals make for them. If my bank only lets me access my account online, if my telecommunications company only lets me do business online, if my doctor only makes my lab results available online, then to disconnect from the internet would mean disconnecting from the individuals, institutions and services I need for everyday life.”
Some are concerned with people in certain segments of society being unable to choose to fully or partly opt out as they wish. An anonymous senior research scholar at a U.S. university’s digital society lab said, “Both statements are likely to be correct. Most people – the poor, vulnerable, dependent – won’t have the means to disconnect. Social and political systems – education, employment, government services – will require them to stay connected. Those educated, independent and privileged enough to prioritize their rights and liberties over public systems will increasingly disconnect or manage their connectedness. Privacy and liberty will become ever more the province of those with economic means.”
You can’t avoid using something you can’t discern. So much of the Internet of Things operates out of sight that people will not be able to unplug completely
A number of these experts raised the point that as connectivity is becoming built into everything, people often do not know what is connected, what is collecting data, who sees the data that are collected and why, and how all of these things are linking to other things. Andrew Walls of Gartner said, “People will remain largely unaware of the degree of connectedness present in the products they select and will merely pick products and services based on personal preferences for comfort, convenience, value for money, etc.”
A significant number will have the illusion of being disconnected [when they actually are not]. Bob Frankston
[they’ll]
[when they actually are not]
Theme 3: Risk is part of life. The Internet of Things will be accepted, despite dangers, because most people believe the worst-case scenario could never happen to them
Many of these respondents point out that optimism bias generally moves people to perceive a potential risk as highly unlikely to harm them. When people ask themselves, often subconsciously, “Do the benefits outweigh the risks?” the answer is generally, “Yes – go for it!” – especially when connection and convenience are the result. The majority in this canvassing predicts that the general public expects that any problems tied to their connectedness will fall primarily upon others, not themselves.
Online security is, by and large, an illusion. And I think we all agree to the illusion together. Maria Pranzo
An anonymous computer software sales engineer replied, “Most people aren’t aware of the complexities of online security and assume it will happen to someone else.”
Daniel Berleant, author of “The Human Race to the Future,” said, “All change comes with risks. You don’t see people moving away from cars (with occasional individual exceptions) because cars are dangerous. The dangers of using digital technologies are lower than for cars and while these dangers will be a continuing concern, they won’t stop the overall digitization trend.”
An anonymous respondent said, “People uncritically accept new things: Drones, self-driving cars, corporate exploitation, terrorist incursions are routed through the internet, control over nuclear reactors. The TV show ‘Mr. Robot’ is extreme and entertaining, but it is pointing to issues that are real.”
An anonymous web developer commented, “Pickpocketing hasn’t made people stop carrying wallets, has it? Unless there is a major attack, affecting literally billions of people … in the near future, more people will be connected. As the number of connected people grows, individual cyberattacks and fraud will probably grow as well. Increased attacks probably will not cause massive disconnect, because the positives greatly outweigh the risks.”
Maria Pranzo, director of development at the Alpha Workshops, replied, “Wow. I’m trying to remember how it was before we were all connected. Before the world knew what was going on everywhere at once. It’s a frightening thought, all of this going away. And yet it’s one that I could be completely comfortable with. But that’s my privilege showing. Online security is, by and large, an illusion. And I think we all agree to the illusion together. We count on good people on the front lines: the makers of our hardware and software. We count on their continuing to advance slightly faster than the bad guys. Most of us do so blindly. Why would that change? I certainly don’t check the plane engine before I get on a flight.”
Stephen Downes, researcher at National Research Council Canada, said, “It is true that attacks, hacks or ransomware concerns impact our enjoyment of modern technology. But it’s important to note that what they impact is almost exclusively our enjoyment of modern technology. A person choosing to disconnect from modern technology suffers the same fate as the person who has been hacked. They lose the enjoyment of modern technology. So disconnecting from technology isn’t a viable response to attacks, hacks and the rest. People won’t be looking to withdraw from modern technology, they will be looking for better and more secure modern technology (to a point; as people’s choices of passwords such as ‘123456’ show, they are willing to sacrifice a certain amount of security for a certain amount of convenience. Indeed, if anything forces people off new technology, it will be the security measures, not the crimes).”
Theme 4: More people will be connected and more will withdraw or refuse to participate
A share of the experts in this canvassing think that the future will bring far greater connectivity for most users and that – at the same time – a notable number of people will cut back their ties to connected things or withdraw from that world. They also imagine scenarios where people try to modulate their level of connectivity, being embedded to some degree in the connected world and, to some degree, also withdrawing from it.
Some will embrace it and some will ‘opt out before it happens’
Jeff Johnson, consultant at UI Wizards and Wiser Usability, replied, “My actual answer is ‘both.’ Most people will move more deeply into connected life, but significant numbers will disconnect (or remain disconnected).”
Many will disconnect, but equally as many will double down. Anonymous respondent
Adrian Schofield, an applied research manager, observed, “Both answers apply. Millions will connect because they are at low risk and the convenience factor is high. Thousands will disconnect because they become targets or they fear becoming targets. However, fear of losing wealth has never stopped the relentless pursuit of wealth.”
Wendy M. Grossman, an independent writing and editing professional based in London, said, “As we become more sophisticated about and used to these technologies, we will (I hope) make better-informed decisions about which ones we use and how. … As I watch the way IT is developing, I’m increasingly dubious about how far I want to let it – and the concomitant exposure to potential surveillance – penetrate into my home life. Some of this is because I’ve been online for 25 years and I write about security – I’m distrustful enough that I do almost no online banking and don’t use my smartphone for anything that would expose any of my financial accounts. I’m in the fortunate position of not needing to do these things, so I don’t. I think in the short to medium term we’re in for a lot of grief as legacy manufacturers who know nothing about security add wireless connections and computational power to everyday objects; there’s going to be a big mess one day soon when governments start demanding that the data collected by smart TVs, robots, etc., be retained for use by law enforcement and security services. It’s simpler (to me) to opt out of that before it happens.”
An anonymous employee of the U.S. National Science Foundation wrote, “Both answers are true, since 5% to 10% disconnecting is a significant number.”
An anonymous respondent said, “All devices will become connected by default. It will take an effort to disconnect. But more people will become distrustful of the IoT. It will cause a large culture clash.” And an anonymous network architect observed, “I actually think both are true, possibly resulting in a bifurcation in our social structure.”
John Paine, a business analyst, commented, “There will be a statistically significant number of people who will deliberately disconnect to the extent possible, but overall connections will increase. I expect that a premium will begin to come into play for purchasing ‘disconnection’ as a feature for goods/services in the future.”
An anonymous respondent replied, “The answer is both/neither/it will balance out. Many will disconnect, but equally as many will double down. For every tin-foil-hatted neo-Luddite moving to an island with a telegraph, so to speak, there will be someone gleefully enjoying their networked toaster and toilet. The only thing that might tip the balance more toward disconnection would be an IoT-related infrastructural disaster.”
Right now the IoT isn’t that grand, so why worry either way?
A share of respondents expressed a low level of confidence that the IoT or the security of the networks will advance much in the next decade. Those whose responses generally referred to consumer-oriented applications such as “smart-home” items tended to find them to be less than worthy of sacrifice of one’s privacy or safety. They don’t think IoT uptake will live up to expectations, but they generally are not considering larger systems in the IoT such as transportation, environmental services and finance.
Grant Blank, a sociologist and survey research fellow for the Oxford Internet Institute, said, “The question seems to assume that most people own devices that are part of the Internet of Things. This is currently false. People will generally stay away. There are two reasons: 1) Security is being done badly on the Internet of Things. This seems unlikely to change quickly. 2) Companies are behaving in ways that discourage participation. Major case in point is that Nest recently decided to turn off the servers supporting a whole line of devices, making devices costing $100+ into useless bricks. The bottom line is that the Internet of Things is more useful for companies than for consumers. Consumers will generally stay away.”
An anonymous respondent commented, “I don’t believe the Internet of Things will really become reality. The infrastructure is not good enough and the high number of manufacturers will create lock-ins. The threshold for citizens will be too high – unless they commit to one manufacturer and buy everything from it.”
An anonymous scientific editor replied, “It’s hard to know/guess which way things will go. For me personally, I back away from this stuff as far and as fast as I can, but I’m not sure how many other people will be inclined to do the same. It’s entirely possible that most people will find these ridiculous and dangerous new toys irresistibly compelling. Really though, it’s beyond parody. ‘Smart TV’? C’mon, you’re having a laugh. How might governments and technologists respond to make things more secure and safe? Well, air-gap them, obviously. Very little of this stuff ever needed to be networked in the first place. Cellphones: Good. Highway traffic flow control: Good. An app that controls the light switches in your home: Not so much. As for an automobile controlled by a computer: If it’s an autonomous self-driving car a la Elon Musk, then sure, recent fatality notwithstanding; if it’s a regular car, then OK, there are pros and cons for digital vs. analog; if it’s a regular car with a networked computer, hell no! There’s absolutely no upside to that whatsoever.”
An anonymous senior fellow at an organization that examines the future of privacy issues replied, “People may adopt, then disconnect based on experiences. For example, I don’t see the point in a refrigerator with a 21-inch display in the door, and a lot of the other IoT features seem like overkill. For sensors, horror stories about surveillance may deter use. Connected and driverless cars present challenges with the first fatal crash. It will be interesting to see what happens.”
Theme 5: Human ingenuity and risk-mitigation strategies will make the Internet of Things safer
Many respondents expressed confidence in the evolution of methods by which outside regulators, as well as developers of the software, hardware and networks undergirding the IoT, will build in some method of dealing with constantly emerging security, safety and civil liberties issues.
It’s an arms race, for sure, but I’m confident that we will evolve better security. Jon Lebkowsky
Indeed, regulators have just started to consider recommendations in this fast-evolving setting, moving slowly and not forcefully. The Food and Drug Administration’s (FDA) guidance for management of cybersecurity in medical devices was issued as a draft in January 2016 but not officially released until a year later. The recommendations are nonbinding – more like suggestions. And when the Federal Trade Commission (FTC) announced in January 2017 an IoT “Challenge to Combat Security Vulnerabilities in Home Devices” some experts worried that the top prize for winning submissions was a modest $25,000.
An anonymous futurist wrote, “The vulnerability of networked devices is a technical issue. The original inventors of the internet are basically good people, so they did not recognize all the ways that their devices can be exploited. As the bad actors expose more problems, they will be fixed. I expect that networked devices will become as reliable as our electric power grid today. It will occasionally go out – and it will be a catastrophe. But we will survive.”
Effective regulatory and technology-based remedies will emerge to reduce threats
Pamela Rutledge, director of the Media Psychology Research Center, commented, “The advances in technology will be accompanied by improved security. That is the only way companies and organizations can protect the economic investment in connected products and services; it is the only way connected services can continue to deliver value. There will always be some who choose to self-regulate by withdrawal, but most will learn new skills of self-management and be willing to exchange the currency of personal data and privacy to get the most value from the products available.”
[High-Assurance Cyber Military Systems]
Jon Lebkowsky, CEO of Polycot Associates, said, “It’s an arms race, for sure, but I’m confident that we will evolve better security. And I’m pretty sure the negatives along the way will not diminish trust to the point that people disconnect in a big way.”
[thanks]
An anonymous respondent commented, “It feels like an inevitability that some series of high-profile ransomware attacks, e.g., turning off an IoT pacemaker to take out a U.S. senator or CEO, will happen, because human greed is not a force we’re likely to eliminate in the near term. That said, I doubt the backlash against that kind of attack will be disconnection, it’ll be the solidification of security standards and ‘trusted’ brands of devices. There will always be both greedy bastards and the tinfoil hat brigade, but my hunch is that both sets will remain on the fringes, with the middle 90% opting to make smarter decisions about who/what has access to certain information/devices.”
Governments should be doing more to regulate negligent companies, punish bad actors
As citizens become more educated about the network and how things are connected, more pressure will rise to provide safe and secure spaces. Anonymous staff member at a state university
[random data used as an additional input]
An anonymous staff member at a state university said, “We have had great moments of mistrust, which have stemmed largely from an underestimation of threats and a misunderstanding of the network and how they work. As citizens become more educated about the network and how things are connected, more pressure will rise to provide safe and secure spaces. However, organizations that exploit the data and the network should be found and swiftly punished instead of being tacitly ignored as we see so often.”
Demian Perry, director of mobile at NPR, observed, “The problem with IoT devices is not that these devices are inherently less secure, but that the space is too new to have a mature security infrastructure. The market is likely to weed out insecure products over the long term, but it might also be helpful to have regulatory review over certain product categories, similar to the way the FDA manages food safety, or the role the National Transportation Safety Board is now playing in autonomous vehicles.”
Jason Hong, associate professor at Carnegie Mellon University, commented, “In the short term, we will see a lot more IoT-based attacks, especially ransomware attacks. However, organizations are already taking steps toward improving the situation. For example, the FTC has issued reports on IoT security and is asking the top manufacturers about their cybersecurity practices. Over time, I expect there to be more centers of excellence to help disseminate best practices for coding and managing IoT systems. Researchers will also come up with better ways for managing collections of devices as well as protecting low-end devices. It’s also likely that insurance companies will help improve the state of the art by having higher premiums for IoT companies that don’t have good cybersecurity practices. Most importantly, cybersecurity is a known issue, and both IoT manufacturers and consumers are becoming savvier about the risks. So while there will be a lot of growing pains, I’m optimistic about the future of IoT.”
Richard Forno, senior lecturer of computer science and electrical engineering at the University of Maryland, Baltimore County, said, “As a career internet security professional, I continue witnessing people rushing to embrace the latest and greatest thing or gadget or service without thinking about the possible ramifications to their security, privacy or resiliency. And it’s not just about security or privacy – what if the product vendors for your IoT-enabled things go out of business or decide to make their product incompatible with others in the same space? (Which is happening already.) What will users do then? Accordingly, security practitioners and educators at all levels will constantly struggle to inform the public about these risks in ways it can understand easily and potentially address in their respective lives.”
Theme 6: Notable numbers will disconnect
Some 15% of the respondents in this canvassing expect that perceived and real vulnerabilities of the IoT will move people to disconnect. They noted the escalating security and privacy risks posed by connected devices and the complications that occur when fast-changing, fast-growing complex systems are built and networked. Many among this share of respondents seem to have little to no confidence that the builders of the IoT will make security, safety and individuals’ civil liberties their first priority because profit, power and efficiencies always come first, leaving far less investment in the crucial, difficult, expensive and perpetual work of minimizing threats.
Lack of trust, safety and privacy issues and more may move those with fears to withdraw
Expressions of concern, disappointment and resignation are evident in the responses from those who say it is likely there will be some who choose to disconnect in some manner from the IoT. Mistrust is the big factor in these answers, especially when it comes to other humans. Their worries are generally tied to 1) their expectation of harm from criminals and other bad actors; 2) their suspicions about the primary motivations behind the acts of the corporate and governmental bodies they must depend upon to operate these networks and 3) their lack of faith that people can get it all together to plan, regulate, build, monitor, update and maintain such complex systems.
More, and more serious, data breaches are likely to push people away from the Internet of Things. Anonymous respondent
[takes]
An anonymous respondent replied, “I expect that within 20 years it will be very difficult or impossible to buy non-IoT versions of many common items (this is already rapidly becoming the case with televisions). The current norm of poorly engineered, non-updatable, easily exploited IoT ‘security’ will continue, further opening the surveillance window for governments and corporations and creating an even vaster, botnet-armed cybercriminal underground.”
An anonymous respondent said, “More, and more serious, data breaches are likely to push people away from the Internet of Things. Stalkers using home webcams to collect information, breaches of medical records that are used to blackmail thousands and subverted automobiles will drive educated consumers away from insecure systems.”
Joel Barker, futurist and author at Infinity Limited, said, “Disconnection is the only solution to the size of the risk.”
[there will be disconnection]
Corporate intransigence, shortsightedness and misguided thinking create vulnerabilities
Jennifer Zickerman, an entrepreneur, replied, “Sadly, people will continue to connect devices without demanding better security design. Shiny new technology will trump big, dumb security vulnerabilities. Institutions are particularly vulnerable, as they stand to reap the greatest benefit from ‘smart’ devices. We will see situations where hospital equipment, utility systems, even entire buildings are held for ransom. It is most definitely possible to improve security – however, that would involve settling on a common, open-source security standard, which tech corporations are loath to do. (Witness the fragmentation of single sign-on systems.) As long as tech companies continue to look at security as a ‘feature’ rather than as a fundamental operating characteristic, they will be unable to cooperate to build proper security infrastructure. As long as society continues to allow tech companies to reap vast profits in spite of the damage they do to users through a lack of effective security, tech companies will have little incentive to improve.”
There is a limit to the trust people put into their machines. Jesse Drew
An anonymous systems engineer replied, “Corporate greed prevents things from being done well, thus the Internet of Things is a horrifically stupid idea that will drive people back to using technology that can’t be corrupted by corporate greed.”
Jesse Drew, cinema and digital media professor at the University of California, Davis, replied, “There is a limit to the trust people put into their machines.”
An anonymous advocate for international freedom of expression wrote, “I don’t feel confident about the state of data security at the moment, and I fear that putting more data in the hands of reckless corporations will endanger us. Consider the impact of a leak of health-related information – what’s to stop predatory insurance companies from denying coverage?”
An anonymous chief technology officer commented, “Until security improves, a significant number of sophisticated users will disconnect. I’m not going to install a Nest, my next TV will not run apps, even if it costs me more, and I’m not going to get a Samsung internet-connected refrigerator. I will willingly give up convenience until the developers get it right. If they ever manage to.”
‘TMI’ and less-than-stellar performance from complex IoT systems will drive dropouts
Some respondents wrote that people might simply withdraw from connectivity because they are overwhelmed. Among the contributing factors would be information overload; poorly made or overly complex IoT tools and systems; products that do not perform well, lack support and/or are in constant need of updates and patches; and IoT products that are given to new owners without the manufacturer knowing of the switch. As a result, some of these respondents say, people will disconnect to a certain degree or never consciously connect.
Timothy C. Mack, managing principal at AAI Foresight, wrote, “At present, the Internet of Things is more a series of missteps than a grand design, if for no other reason than many of the large players are competitors versus cooperators and accepted protocols are still not agreed upon. As well, the ‘gold rush’ quality of such areas as ‘smart homes’ has led to shoddy design and poor construction of the physical and the digital aspects of this brave new world. As for the loss of critical safety and security through networks trying to interconnect and protect and the same time (with largely the same tools), we should expect many more disappointments in the IoT development saga.”
Ryan Sweeney, director of analytics at Ignite Social Media, commented, “We’re going to see two groups start to emerge within the next decade: those connected and those unplugged. Being connected can be burdensome to users as they face information fatigue. Bret Easton Ellis wrote a book titled ‘Lunar Park’ that provided a fascinating take on the concept. (Spoiler alert!) Ellis depicts a world where kids are so saturated with information they become bored with and numb to technology so they run away and start a community of their own. In Dave Egger’s book ‘The Circle,’ (spoiler alert) a character strives to escape the oppressive nature of an omni-connected dystopian future and finds death to be the only way out. Exaggerated? Yes. Conceptual plausibility? Definitely. Meanwhile, as algorithms become more efficient and technology more omnipresent and accepted, there will be continued growth of plugged-in users. Governments will need to focus on protecting the connected user, as acts of terrorism will likely shift to the digital when the damage potential is great enough. When everything is connected and relies on said connectivity of other sources, disconnecting one system could result in a significant freeze of efficiency. If, for instance, within this decade automated cars become standard that system could become compromised resulting in anything from an economic shock to massive loss of life by collision. The sci-fi nerd in me wonders if, in several decades, this will result in a new type of class system.”
Pete Cranston of EuforicServices.com said the machines will manage the complexity, observing, “There will be scares, genuine disasters, but the potential gains from interconnectivity are so great that we will continue to lurch into a future where we will have to confront issues of independent machine-machine decision-making (aka machine intelligence, but actually more to do with interlocking algorithms exponentially increasing the complexity of machine response patterns) much more actively.”
Theme 7: Whether or not people disconnect, the dangers are real. Security and civil liberties issues will be magnified by the rapid rise of the Internet of Things
Many respondents to this canvassing said the dangers of the IoT are real and present a daunting challenge. They are certain that in the future there will be more attacks with more devastating results as billions more things and people become interconnected online and systems become more complex and difficult to manage. Many have deep concerns about the protection of civil liberties in a world in which so much granular data is continuously collected and databased, especially considering the fact that the “threat environment” created by this complex networking is high.
Threats are likely to turn into attacks and other acts, possibly some violent
An anonymous engineer at Cisco commented, “It is inevitable that more people will be connected more and more, but we do not expect the security, which is a cat-and-mouse game, to significantly improve relative to the number of things getting connected. People will lose their lives due to criminal exploits of vulnerabilities.”
As physical attacks become more public, people will understand the need to take greater responsibility for their own cybersecurity. John Howard
An anonymous programmer and data analyst wrote, “Most people are totally oblivious to the fragile and easily pierced nature of the Net and the total lack of protection of their medical/financial information. They will continue to not care or understand the issues and will move more deeply into connectivity. Attacks on power infrastructure, automated vehicles, airplanes, food supplies are all unfortunate consequences of the IoT.”
[a gamer term meaning “beaten handily”]
John Howard, creative director at LOOOK, a mixed-reality design and development studio, commented, “The growth of IoT, along with 3D printing and VR, will further erode the digital/physical divide. Physical peril (real or imagined) will put greater emphasis and opportunity on network security. … As physical attacks become more public, people will understand the need to take greater responsibility for their own cybersecurity.”
The rise of the IoT and security concerns amplifies worries over civil liberties
Connected cities will track where and when people walk, initially to light their way, but eventually to monitor what they do and say. Marti Hearst
Some respondents expect that because the risks associated with the IoT are high, that will compel greater surveillance by governments. Advanced artificial intelligence tools will be able to monitor, analyze and pass judgment upon nearly every detail of any individual’s life via the data collected by the IoT. Sentiment analysis can be applied to create a profile of people’s character and intentions; experts say such programs will enhance security and endanger civil liberties. A number of these experts worry that those who control the algorithms will begin to even more deeply exploit the constantly multiplying ways in which they can monitor users’ behaviors and emotions and even predict and/or manipulate how people behave. Some experts say if the brain-to-internet interface were to become a reality, this type of spying could possibly capture and process human thought. It is a sci-fi nightmare brought to life. An anonymous respondent described a worst-case scenario, writing, “It’s the tragedy of the commons: The individual incentives are great (better health, more convenience, saving money) while the long-term consequences for society are grave (loss of privacy, autonomy, safety in one’s own home).”
Marti Hearst, a professor at the University of California, Berkeley, replied, “Just as the pervasiveness of cellphones forced the phasing-out of pay phones in public places, it will become impossible to opt out of the oncoming connected world. People’s businesses, homes, cars and even their clothing will be monitoring their every move, and potentially even their thoughts. Connected cities will track where and when people walk, initially to light their way, but eventually to monitor what they do and say. The walls of businesses will have tiny sensors embedded in them, initially to monitor for toxins and earthquakes, and eventually to monitor for intruders and company secrets being shared. People currently strap monitors on their bodies to tell them how many steps they take. Eventually, all fluids in and out of bodies will be monitored and recorded. Opting out will be out of the ordinary and hugely inconvenient, just as not carrying a mobile device and not using a fast pass on the highway are today.”
T. Rob Wyatt, an independent network security consultant, wrote, “Functionality trumps lack of security every time. We develop new function almost without regard to security and then discover we cannot retrofit it after the fact. A recent court ruling stated that we should no longer have any expectation of privacy in our internet-connected devices. Considering that we now have forks, toothbrushes, health monitors, mattresses, sex toys and more connected to the internet, this ruling has profound implications to personal life, privacy and checks and balances to government intrusion and control. The ruling went almost unreported and no public outcry was raised over it. No public backlash will occur so long as the toys are shiny.”
An anonymous respondent observed, “It is a huge invasion of privacy. The Internet of Things is not something I want to participate in fully. Only in very limited ways that I can control. But I am older, and wary. Younger folks who have grown up with technologies may not care, so interconnection will grow. I’m still going to buy a TV monitor without a camera, because I don’t want that part of my life camera-enabled. I don’t want my fridge enabled. I don’t really want much of anything enabled. I want privacy.”
An anonymous computer science professor at a Swiss university wrote, “The main issue with connected objects is the potential to trace people, their actions and activities, or to hack objects and change their behavior. We should avoid having completely centralised systems where each event is recorded and sent to governments or surveillance bodies.”
Mary Chayko, communications and information professor at Rutgers University, replied, “While cybersecurity has become a critical challenge for governments, psychological security – a sense of safety and rootedness – becomes perhaps the premier challenge for individuals. As we see our devices and world become ever more tightly networked and interconnected and recognize the inherent security vulnerabilities in such a system, we become more psychologically and emotionally vulnerable. My hope is that we will address this, as we have so many other issues in the digital age, in community with one another – coming together (often online) to better understand our common human responses, needs and frailties, and to develop stronger, more secure systems and selves.”
Responses from additional key experts regarding the future of connectivity in the age of the Internet of Things
This section features responses by several of the many top analysts who participated in this canvassing. Following this wide-ranging set of comments, a much more expansive set of quotations directly tied the seven primary themes begins on page 40.
‘Whose intelligence? Whose control? … How can we monitor the monitors?’
Barry Chudakov, founder and principal at Sertain Research and StreamFuzion Corp., replied, “We can now unleash the power of all brains, all consciousness – both somatic and artificial – to solve problems and improve the human condition. This is truly a remarkable development. … Bruce Schneier says the Internet of Things, with the computerization of everything, will be the world’s biggest robot. This everything-everywhere ‘robot’ – a concatenation of connected things, sensors and actuators – will change the world in ways we cannot predict and will maximize profits for those who control the components. Physical or human damage might be contained … or it could leave nations and governments more vulnerable to hacktivism and cyberterrorism targeting air monitoring, water and electrical infrastructure systems. … Smart and networked also means malicious actors can hack these systems and create mischief and worse. … The Internet of Things is a way of not only connecting objects, but also embedding intelligence into those objects. That intelligence is persistent and will soon be ubiquitous. Very quickly the question arises: How much intelligence? And how much decision-making, or control, can be embedded into those objects? … The mostly likely physical or human damage that will occur when things are networked arises in this area: Whose intelligence? Whose control? How do we, if need be, circumvent it or turn it off? How can we monitor the monitors to ensure no bad actors are trying to harm us using IoT as a weapon?”
Fixes will arise because the cyberphysical space is the fastest-growing part of the economy
Glenn Ricart, Internet Hall of Fame member and founder and chief technology officer of U.S. Ignite, said, “There is tremendous latent potential in greater connectivity – enough potential to force providers and consumers alike to find ways of minimizing the inevitable downsides. Just as Underwriters Laboratories (the famous UL label) was started by insurance companies to minimize losses due to fire and other malfeasance of new electrical technology, I would expect that organizations like Mozilla and Electronic Frontier Foundation and others will create testing programs and labels that will have value in creating trust and reducing vulnerabilities. At some point, the National Institute of Standards and Technology will find that it must turn the majority of its activities to standardization and testing in the cyberphysical space because that is the portion of the economy growing most rapidly.”
‘The attacks will get much worse’ but there are ‘ways to mitigate them’
[Digital Millennium Copyright Act]
A better evaluation and certification system for devices is needed
Henning Schulzrinne, professor at Columbia University and Internet Hall of Fame member, commented, “Consumers currently have no reasonable way to judge whether the devices they buy are designed according to common security practices, whether and how they are being tested, how security-related bugs are addressed and for how long after purchase. Nor do they generally know what kind of data the vendor stores where, shared with whom and for how long, and whether those systems are regularly tested by independent third parties. For higher-risk devices that can either do physical harm (cars) or can cause significant loss of privacy (in-home cameras) or endanger physical safety (door locks), some kind of certification that does not just consist of 10 pages of disclaimers seems necessary.”
Technology has always inspired fears, but ‘people found ways to use them effectively’
Jonathan Grudin, principal researcher at Microsoft, observed, “Previous hardware generations and major software advances gave rise to fears, but people found ways to use them effectively, warranting measures to prevent serious misuse or negative consequences. Why would this be an exception?”
People will demand solutions to problems in the cyber-enabled world
Jim Hendler, professor of computer science at Rensselaer Polytechnic Institute, observed, “Automobile accidents have not kept people from driving, burglary doesn’t keep people from owning houses with nice things in them and workplace violence doesn’t keep people from holding jobs. Society finds ways to control these things, by a combination of social and technical means, and while none are completely removed, they are kept to a level people can tolerate – locks are put on doors, laws are passed, policemen are hired and society adjusts. The cyber-enabled world will need to create analogous mechanisms, which will happen as awareness of threat increases, and impacts will be controlled. There will be a period of adjustment (as bad things happen), followed by a demand for change, and that will motivate (through financial incentives and/or legal penalties) change.”
Risk is a part of life and IoT security will improve
Robert Atkinson, president of the Information Technology and Innovation Foundation, observed, “Most adults in the U.S. drive cars even though it entails risks. Most adults will use IoT devices even though they involve risks because the benefits will vastly outweigh any potential risks. Moreover, as IoT progresses security will improve.”
People will have little choice but to participate in the Internet of Things
Alice Marwick, a fellow at Data & Society, wrote, “Opting out of the Internet of Things will become increasingly difficult, as devices from automobiles to alarm clocks will be equipped with proprietary internet-enabled software. The ability of people to tinker with their own devices, choose whether they want internet connectivity and select non-connected devices will decrease, making opting out onerous, expensive and disadvantageous. This is similar to the body scanners in airports, where one can opt out, but it has a cost. Currently, data breaches are widespread, but the cost of opting out (of, for instance, credit cards) generally outweighs the risk. People will have little choice but to participate in the Internet of Things.’’
Opting out is not viable: How does one ‘disconnect’ from a home, city, airport, health care?
Kate Crawford, a well-known internet researcher studying how people engage with networked technologies, said, “This question assumes that disconnecting remains a socially and economically viable option. For many millions of people, it simply won’t be. Quite apart from the individual use of devices and platforms, the infrastructure of everyday life will be networked. How does one ‘disconnect’ from your home, city, airport or health care system?”
Fixes are hard to conceive, but people might not have a choice
Rebecca MacKinnon, director of New America’s Ranking Digital Rights initiative, wrote, “Innovations in governance, accountability, security and industry coordination (without collusion) are going to need to advance in ways that are hard to conceive at this point in time. People with real security concerns are going to want to disconnect but the question is whether they will have a choice. In some parts of the world, perhaps not.”
‘The likely consequence will be more catastrophic events’
Marc Rotenberg, executive director of the Electronic Privacy Information Center, said, “The essential problem is that it will be impractical for people to disconnect. Cars and homes will become increasingly dependent on internet connectivity. The likely consequence will be more catastrophic events.”
The cost and severity of lapses and breaches will be ‘a constant, ongoing burden for all’
Anil Dash, entrepreneur, technologist and advocate, observed, “People will continue to connect out of necessity, but the cost and severity of lapses and breaches will increase until it’s a constant, ongoing burden for all.”
Newly empowered users will prevail; it is an ‘Age of Amateurs’
[there will be more connection and some will disconnect]
Only choose ‘libre software’-connected devices
The benefits of being connected ‘outweigh the risks’
Jeff Jarvis, professor at the City University of New York Graduate School of Journalism, observed, “It wasn’t long ago that it was said no one would ever put their credit cards online. Then came Amazon. The benefits of being connected far outweigh the risks. There are more than enough worrywarts and regulators to watch over our safety.”
No ‘back-to-the-land’ movement is in sight
John Markoff, senior writer at The New York Times, commented, “I see no back-to-the-land movement on the horizon.”
‘Off-netters’ will get attention but will not add up to much
Mike Roberts, Internet Hall of Fame member and first president and CEO of ICANN, responded, “It has been demonstrated time and again that individuals will trade privacy for convenience. If a new network application promises self-perceived convenience or value, such a trade is likely. Indeed, we see it going on every day. One of the broader issues is how to deal with privacy as a social construct. Much of what we regard as privacy today is an Enlightenment idea that is associated with personal freedom and other human rights. Some regard these as ‘immutable,’ others as fungible in pursuit of a better life. The arguments are not going to be settled soon. Cultures of dissent will persist, and much will be made of ‘off-netters,’ similar to the publicity gained by today’s ‘off-grid’ culture. Probably not a big deal in the grand scheme of things.”
‘New jobs and social processes will emerge to protect the IoT’
Ben Shneiderman, professor of computer science at the University of Maryland, observed, “Malicious attacks by vandals, criminals and terrorists will expand, but increasingly powerful defenses will be built. Some can be centralized and top-down, but bottom-up, community-driven strategies will emerge, along with devoted public defenders (vigilantes). New jobs and social processes will emerge to protect the IoT.”
‘Everything that can be connected to the web will be’
Stowe Boyd, managing director of Another Voice, wrote, “In a world in which connected driverless transportation becomes the ubiquitous and low-cost norm, few will be concerned that occasionally a hacker can take over a vehicle and crash it, especially since tens of thousands die every year in car accidents now. That example will be the instance that proves the general case. Yes, hacking will continue, and corporations and governments will fight it, but meanwhile, the overwhelming majority of human activities and finances will move online, and everything that can be connected to the web will be.”
Those who disconnect will be outliers
[already]
‘Massive work is needed’ to make the Internet of Things function
Randy Bush, research fellow at Internet Initiative Japan and Internet Hall of Fame member, commented, “People will ignore the continuous IoT disasters, and the press will minimize them. We paper over IoT security issues, yet massive work is needed here.”
‘People will just hope that the institutions around them won’t harm them’
danah boyd, founder of Data & Society, commented, “There will be no choice. As a result, many people will just hope that the institutions around them won’t harm them, while some people will feel very acute pain because they don’t fit into the system in an acceptable way.”
This is the early break-in phase; things will get better over time
Doc Searls, journalist, speaker and director of Project VRM at Harvard University’s Berkman Center for Internet and Society, wrote, “The Internet of Things is a misnomer, at least as of today. What we have instead is what Phil Windley, PhD, calls a ‘Compuserve of Things.’ His summary: ‘On the Net today we face a choice between freedom and captivity, independence and dependence. How we build the Internet of Things has far-reaching consequences for the humans who will use – or be used by – it. Will we push forward, connecting things using forests of silos that are reminiscent the online services of the 1980s, or will we learn the lessons of the internet and build a true Internet of Things?’ Connectivity for things today is where connectivity for people and computers were in the 1980s and early 1990s, when the closest things we had to the internet were Compuserve, AOL, Prodigy and other ‘online services’ that didn’t interact with each other. Likewise today we have the Google of Things, the Apple of Things and the Amazon of Things – all of them closed corporate systems. Worse, many of the connected things we are sold today spy on us, usually without our permission. Some cars report our driving to insurance companies. Some Samsung TVs watch and listen to viewers in living rooms, so Samsung can sell that data to other parties for advertising purposes. This is not only appalling on its face, but it will be flushed out by both market resistance and regulations such as the EU’s General Data Protection Regulation. The only way to fully reduce vulnerability to surveillance and other forms of bad acting is to give individuals full control over the things in their lives. Today we are only beginning to evolve toward that end state; but the demand will be there, which is why there will be a business in it, and it will come to pass. Once it does, much better information will flow from people who own things to the companies that make and service those things. And spying won’t be required. Between now and then we will continue to face Dr. Windley’s choice.”
‘When it comes to the Internet of Things and data breaches, winter is coming’
Amy Webb, futurist and CEO at the Future Today Institute, wrote, “Historically, we have not seen a positive correlation between large-scale hacking attacks and significant numbers of people disconnecting from devices or services. After breaches at some of our largest retailers and entertainment providers, such as Sony and Target, consumers went right back to paying for their goods and services. When it comes to technology, if it makes our lives easier, we will continue to use it, even when risk is associated. Look no further than Uber, a service that changes its prices regularly, sometimes with increases up to five or six times above what they would be otherwise. We might complain, but the fact is that we continue using the service, even when it makes no financial sense. Technology can be like junk food. We’ll consume it, even when we know it’s bad for us. There is no silver bullet. The only way to effectively prevent against malware and data breaches is to stay continually vigilant. To borrow an analogy from ‘Game of Thrones,’ we need a ‘Night’s Watch’ for security. Because when it comes to the Internet of Things and data breaches, ‘winter is coming.’ Organizations must hire enough knowledgeable staff to monitor and adjust systems, and to empower them to keep pace with hackers. IT and security staff must be willing to educate themselves, to admit when they need help and to demand that executives make decisions proactively.”
‘Most people don’t care about security or privacy until they have experienced a breach’
Brad Templeton, chair for computing at Singularity University, wrote, “Few will disconnect even if there are strong arguments for it. (Self-driving cars will be only marginally connected to their HQs due to security concerns.) When the connections are set up by security pros, they will be more minimal. When set up by the public they will be promiscuous. We need to completely replace our existing operating systems (Windows, Mac, Linux, Android, etc.) to actually make these devices safe, and we must limit their connectivity, but the convenience that comes from not doing those things will win, since most people don’t care about security or privacy until they have experienced a breach.”
‘If such systems prove to be unreliable, people will leave in droves’
Vinton Cerf, vice president and chief internet evangelist at Google and Internet Hall of Fame member, wrote, “This will happen if devices come on the market that require online or at least local communication and programmable control. There are many risks that reliability and safety will suffer unless the makers are diligent about protecting user interests. It could be impossible to escape increased connectivity. Look at present dependence on Google Maps or generally on mobiles and apps in the last 10 years. Reliability will be key. If such systems prove to be unreliable, people will leave in droves. So that’s a primary requirement. Safety is also a primary requirement. Privacy, security are part of the mix but the top two are reliability and safety.”
Be less concerned with hackers and more concerned about the ways data will be used
Judith Donath of Harvard University’s Berkman Klein Center for Internet & Society wrote, “People will move more deeply into connected life – and they also will be moved there whether they want to be or not. The connection of the physical world to information networks enables the collection of an unimaginably vast amount of data about each of us, making it possible to closely model how we think and to devise increasingly effective ways of influencing how we act and what we believe. Attaining this ability is extraordinarily valuable to anyone with something to sell or promote. The crucial key is getting people to provide the data, and it’s not surprising that we’re already seeing many once stand-alone objects (watches, heart rate monitors, thermostats, cameras, house keys and so on) turn into data-collecting network devices. My concern with the safety of things that are part of deeply connected world is not about its security and the dangers of being hacked (though those are real, and quite serious) but with the dangers that come with their intended uses: collecting a vast amount of intimate data about each person, while weaving themselves into everyday life as a source of great convenience and pampering.
The internet will become more like a utility
David Lankes, professor and director at the University of South Carolina’s School of Library and Information Science, said, “There is an interesting shift when a feature or service becomes a utility. It becomes simultaneously expected and invisible. You flip on the light switch and you simply expect power to be delivered while simultaneously becoming less aware of how that happens. You expect roads to take you to a destination but have little knowledge (or concern) with what the road is made of (concrete, asphalt, new materials). This leads to a series of troubling issues. Take those roads. We assume, as a utility, they are available, but don’t know specifics. Specifics like bridges aging out of service. We only become aware of the importance of both availability and service assurance when something goes wrong. Even then, we still drive on the next bridge assuming that the failed one was an anomaly, or that a failed bridge will spur action. The Internet of Things is nothing more or less than the evolution of the internet to a utility. We don’t think about our refrigerators having IP addresses, or our cars linking to Wi-Fi because we simply assume they will. The value we get is too high not to take the risk – particularly because the risk is hidden or minimized.”
Security must improve, but ‘need will drive manufacturers to provide secure solutions’
Galen Hunt, partner research manager at Microsoft Research NExT, urged, “The security of IoT must improve. As more devices attach, consumers and enterprises will grow in their understanding of the profound need for secure systems; this need will drive manufacturers to provide secure solutions.”




